Cisco Umbrella: Secure Internet Gateway (SIG) Essentials Package
Taking a new approach to Network Security

The new normal - decentralized networks
Exploding SaaS usage. Proliferating remote locations. Swelling ranks of roaming workers. It's the new normal, and it's driving a transformation in enterprise security and networking. The wide-scale use of cloud applications has become fundamental to business operations. New research from ESG notes that 86% of organizations today are extensively or moderately using public cloud computing services (Saas or IaaS).
Security challenges
With these shifts, centralized security policy enforcement diminishes, and the risk of successful attacks or compliance violations increases. Security teams struggle to keep up. Many organizations have lots of separate point solutions that are difficult to integrate and manage. Sixty-four percent of organizations reported that network security at the edge has become more difficult than it was 2 years ago. And, 26% said that the number of disparate network security tools was a major contributor to that increased difficulty.1 These point products are generating thousands of alerts, but many go untouched. In fact, 52% of daily alerts are not investigated.
IT security pain points
Network decentralization and the accompanying security challenges underlie the top IT security pain points with which organization of all sizes, in all industries grapple. To lessen the pain (and create new value) security leaders are moving toward consolidated, cloud-delivered solutions that provide broad protection for users while also simplifying the environment, reducing bandwidth costs, and relieving resource constraints.
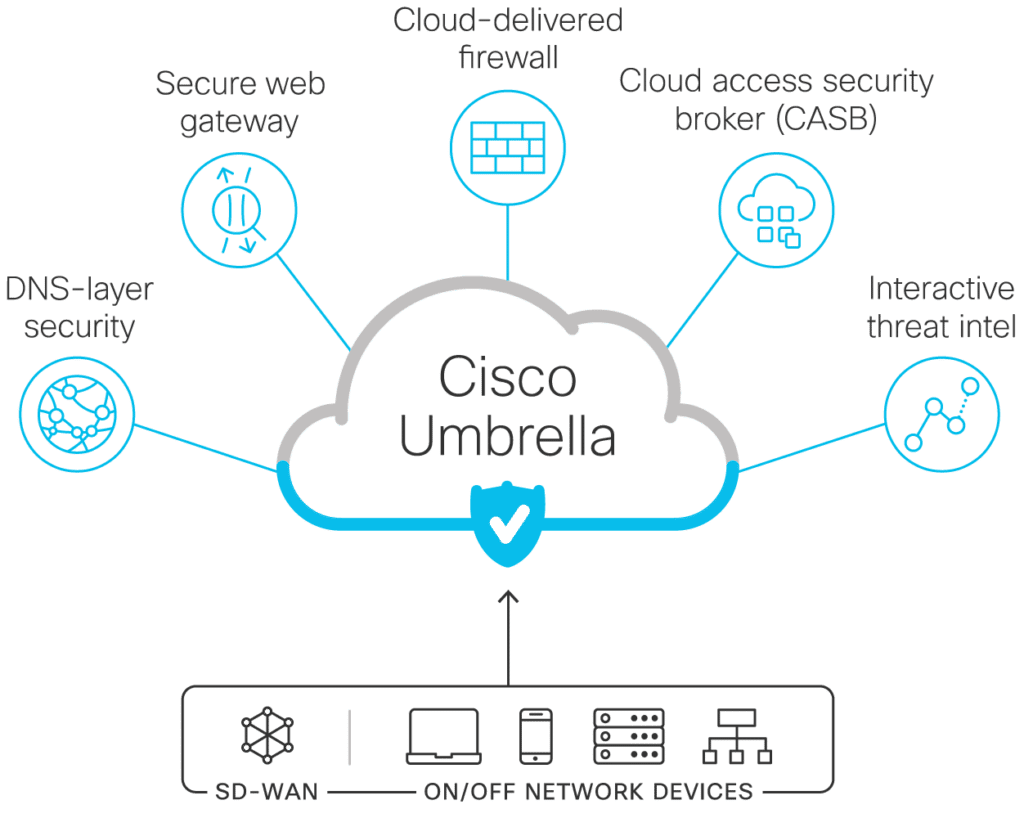
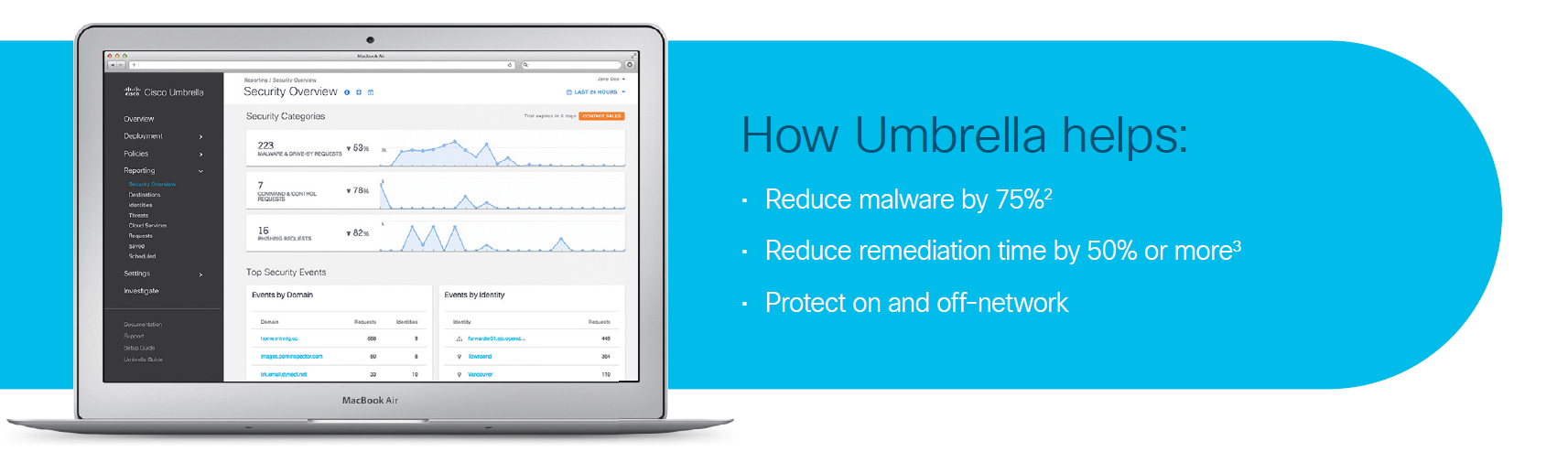
Solution: Cisco Umbrella - SIG Essentials package
The Umbrella Secure Internet Gateway (SIG) Essentials package offers a broad set of security functions that until now required separate firewall, web gateway, threat intelligence, and cloud access security broker (CASB) solutions. By enabling all of this from a single, cloud-delivered service and dashboard, Umbrella significantly reduces the time, money, and resources previously required for deployment, configuration, and integration tasks. It can be integrated with your SDWAN implementation to provide a unique combination of performance, security, and flexibility that delights both your end users and security team.
Top 3 reasons organizations are looking for a SIG:

Improved security coverage and visibility
- Broad security coverage across all ports and protocols
- Security protection on and off network
Centralized/consistent policies across remote locations
- Rapid deployment and flexible enforcement levels
- Immediate value and low total cost of ownership
Better performance and user satisfaction
- Single dashboard for efficient management
- Unmatched speed and reliability with hybrid Anycast

Major components of Umbrella
The following components are integrated seamlessly in a single, cloud-delivered service:
DNS-layer security
This is the first line of defense against threats because DNS resolution is the first step in internet access. Enforcing security at the DNS and IP layers, Umbrella blocks requests to malicious and unwanted destinations before a connection is even established - stopping threats over any port or protocol before they reach your network or endpoints. As a cloud-delivered service, it:
- Provides the visibility needed to protect internet access across all network devices, office locations, and roaming users.
- Logs and categorizes DNS activity by type of security threat or web content and the action taken - whether it was blocked or allowed.
- Retains logs of all activity as long as needed, ready to recall for deeper investigation.
- Can be implemented quickly to cover thousands of locations and users in minutes, to provide immediate return on investment.
Secure web gateway (full proxy)
Cisco Umbrella includes a cloud-based full proxy that can log and inspect all of your web traffic for greater transparency, control, and protection. Highlights:
- The ability to efficiently scan all uploaded and downloaded files for malware and other threats using the Cisco AMP engine and third-party resources
- Full or selective SSL decryption to further protect your organization from hidden attacks and time-consuming infections
- Granular app controls to block specific user activities in select apps (e.g. file uploads to Dropbox, attachments to GMail, post/shares on Facebook)
- File type blocking (e.g. block download of .exe files)
- Detailed reporting with full URL addresses, network identity, allow or block actions, plus the external IP address
- Content filtering by category or specific URLs to block destinations that violate policies or compliance regulations.